In previous article: Effective Git Branching Strategy, I discussed Git branching strategy and how you can follow best practices to manage your code and builds.
In this article, I will show how you can protect your git branches and restrict them by implementing the best practices.
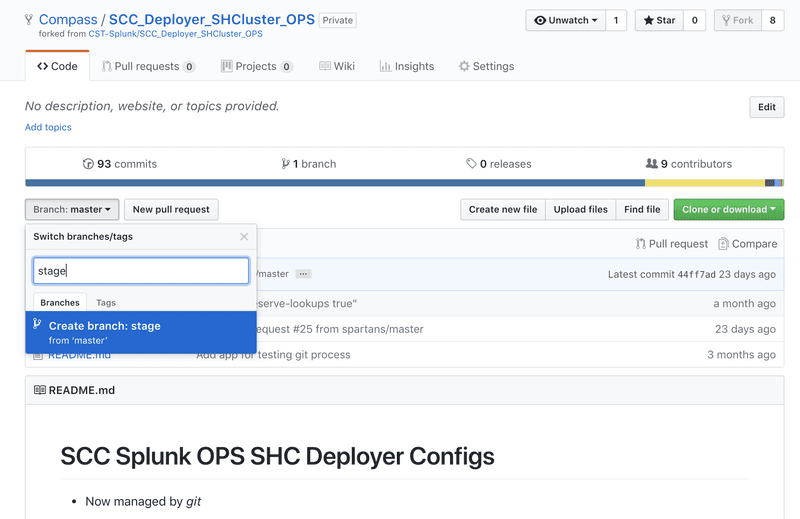
Create Stage Branch
Open your Master branch. On left hand drop down, you can see only Master branch. Start typing “stage”, and it will give you an option to create that branch. See image below:
Protect Your branches
Here, we are going to restrict our two branches: master and stage for two things:
- Any code merge will require code review
- Only specific person can merge the code
- Click on Settings tab on your repository.
- Click on Branches section from left side menu.
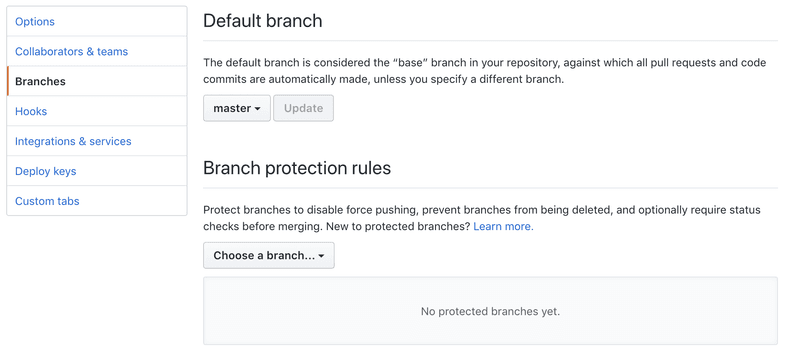
- Click on Branch Protection Rules, and click on Master:
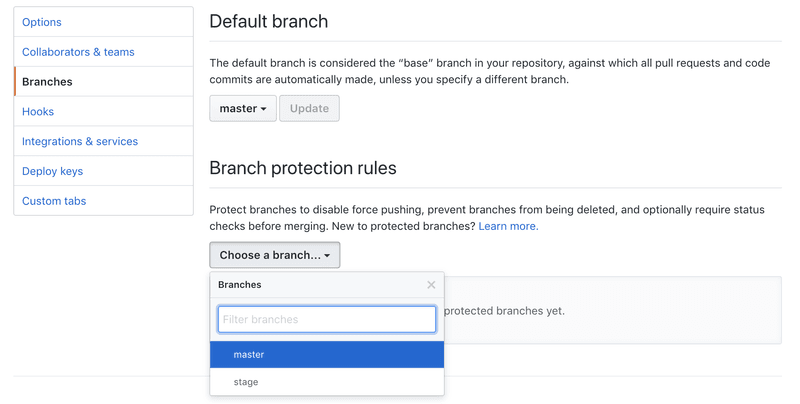
Check on Two options: “Protect this branch”, and “Restrict who can push to this branch”, and do appropriate settings:
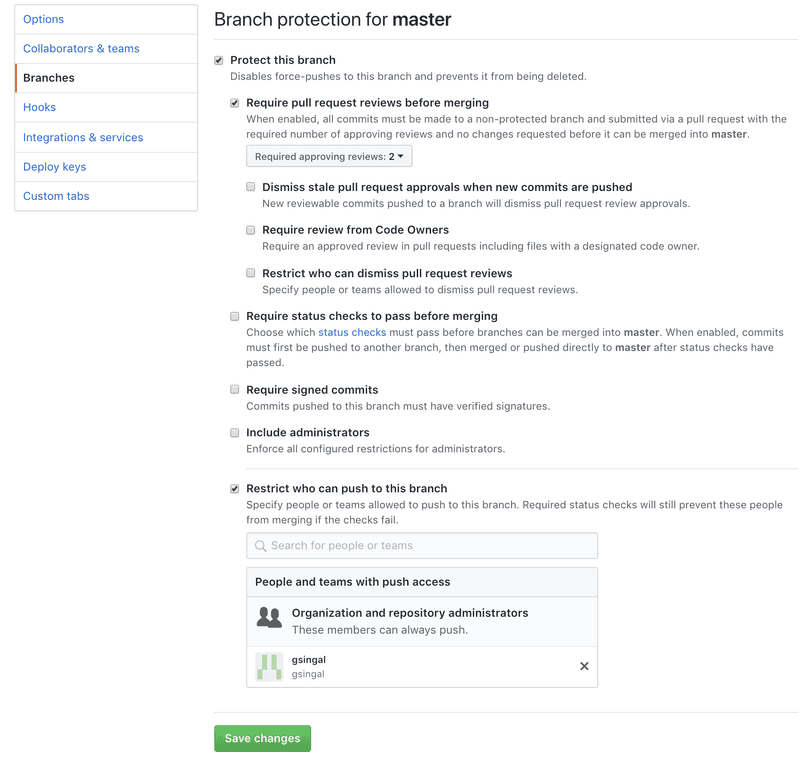
Click on Save changes.
Similarly do this for Stage branch.